The same threat actor has leaked larger amounts of data from LinkedIn dated 2023. They claim this new data contains 35M lines and is 12 GB uncompressed.
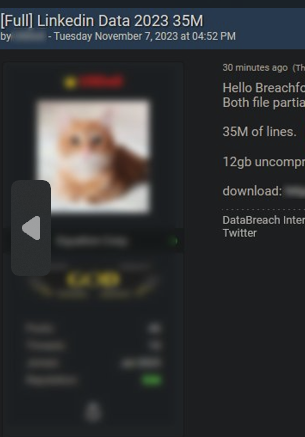
Troy Hunt, the Have I Been Pwned person, has a very informative analysis of the breach that was not a breach, turns out nothing actually “leaked” from Linkedin, it’s a mix of scrapped and generated stuff
Yeah but that doesn’t get the clicks!!!11one!
It says it’s scraped and not leaked
Well, fuck. This was the ONE social media site that I put my data on, and that was out of necessity (job hunting). I know it’s not the same, but this sort of feels like the Equifax breach.
I stopped using LinkedIn several years ago when it was turning into some hideous social media thing rather than just a place to keep an updated cv. I took a look at it six or so months ago and Jesus Christ, what the fuck happened?
It appears to now just be filled with people desperately trying to convince other people that they’re an expert when in reality they’re just talking to themselves and no one’s really listening.
It’s so stupid, but definitely can be helpful professionally to maintain a profile there. Depends on your experience and what field you’re in, of course, but recruiters seem to use it a fair amount.
Definitely don’t use it for the garbage social media aspect (it’s like some weird crowd-sourced Chicken Soup for the Soul shit??) However, I’ve been convinced of its utility after getting a new job through a recruiter there without even looking. The process was sooo easy compared to applying for jobs the traditional way. Icing on the cake was that it came with a 50% raise and was for a position I would never have applied for on my own but I love it. Maybe it was lightning in a bottle, but I figure doesn’t hurt to keep up a page just in case another good opportunity comes along. If nothing else, the recruiters I hear from give me a sense of how hot the market is and what kind of jobs my profile is pinging me for in case I want to make tweaks.
For sure, there’s definitely utility to having one. I just got fed up with constantly getting pinged by recruiters that were clearly bots as well as all of the @ mentioning on said ‘chicken soup for the soul’ bullshit posts.
Oh god yeah, I feel that. I’d have a harder time keeping mine up if my colleagues were actually attempting to engage with me on it haha.
Its all HR people constantly job hunting by sharing the equivalent of those “hang in there” wall posters from the 90s and adding a paragraph about what it takes to make it in the workforce.
Ill make one of these bullshit posts now.
Suggested:
In school my old teacher Mr. Gerry would perform the elephant toothpaste experiment. This got me thinking. The glass beaker is like the job market and the chemicals mixed together is like your marketable skills that grow to fill the needs of the job market. In my 16 years as a human asset coordinator I’ve come across many difficulties that required shifts in how I approached the job market. Be like the elephants toothpaste and explode into the market beeeeyaaaaa

It still works as intended if you ignore all that and keep your head down. I get a fair amount of relevant offers and I got rather nice jobs through it over the last 15 years.
And everyone is a *manager or “executive of”. Even a McDonalds burger flipper is “executive in charge of protein rotation”
If it’s any consolation, LinkedIn is notoriously terrible at this, so your data was probably out there as early as 2016 and almost certainly after 2021, when they managed to get hit with similar breaches twice in the same year.
deleted by creator
And we share real background information, very specific details. This could lead them to our friends and colleagues!
But I’m not sure it can be called social media, though, but if you are looking for social media platforms that can avoids data leaks, and don’t ask for your personal info when register, WireMin and Damus are both good choices.
Speaking of which, we should have a version of LinkedIn that is decentralized!
deleted by creator
deleted by creator
linked in that is decentralized
Now you shut your damn mouth, let’s just let Linked In die like it was always supposed to. It’s not some sort of positive networking platform, it’s just a platform that reinforces the old boys club, with some cringey posts from people who are trying to hard.
It’s not an actual leak. It’s mostly scraped data and fake addresses.
Same here, fuck.
What private info is on LinkedIn? I thought the whole point was to make your resume public and get found by employers.
Yeah it’s the only public social media I have with any personal information. If it leaks I’m fine with that because I use VPN and even have my email alias on there.
LinkedIn sells the info themselves, they don’t let the general public easily scrape/access it
Can someone check if my password is there? It’s ‘dupa.7’. Thanks.
dupa.7
https://haveibeenpwned.com/Passwords confirms that is has been hacked 11 times.
Ok, changed to ‘dupa.8’. Thanks.
Or the most secure one: hunter2
What’s that? All I see is *******
I see Lemmy has implemented Reddit’s security settings. Impressive.
RedditIRC ftfy
s e c u r i t y
This password has been seen 2,265 times before
I’m excited for my class action award of $3
deleted by creator
What’s so good about milk from Malta?
Figures. The only way to get someone interested in my linkedin account is for them to steal the data.
Let me know if you see anything you like. I didn’t put it on there but I’m also proficient in bocce ball
I bet they won’t pay attention: you did not say if wooden or plastic bocce! C’mon!!
The jokes on LinkedIn. T-Mobile already has my social security number, birth date, and other important information on the dark web, thanks to their security breach.
Don’t forget Equifax, assuming you are in the USA
Strangely enough, that data doesn’t seem to have surfaced anywhere. There’s a decent chance it was stolen by a nation-state actor using it for espionage.
Don’t forget the OPM hack in 2014, also assuming you’re in the USA and received a military/government background check.
Don’t forget Equifax, assuming you are in the USA
I mentioned T-Mobile because I had gotten notification from AAA/ProtectMyID service that I was signed up for free after one of their breaches, that my information from the T-Mobile incident what was on the dark web. The scan service specifically mentioned T-Mobile.
But yeah you’re right, I knew also that Equifax had problems as well.
Slightly refreshing from them selling your email to spammers as soon as you signed up.
How do you mean? Are you confusing recruiters reaching out to you (which is the whole point of the platform) with spammers?
I would argue recruiters sending me mass generic emails for job offers only partially related to my field is, in fact, spam.
Agreed, but that’s on the recruiters, not on the platform.
“I’ll give this guy your name, contact info, and everything else I have about you, and I take no responsibility that he won’t call you in the middle of the night or visit your house. All good here, yeah?” - LinkedIn
Motherfucker, if LinkedIn were one of my friends, he’d get punched every time a recruiter contacted me despite me setting my options as “not looking for jobs atm”. I want you to point out the exact LinkedIn fuck whose job it is to get punched for this instead, please and thank you.
Wow, ok. Ignoring your apparent refusal to potential salary improvements, you can always turn off notifications, hibernate your account, close your account, or filter emails from LinkedIn, if it’s such a big deal to you.
Nope, at one point I created a LinkedIn account and my email address immediately started getting spam.
I use unique emails for things. Technically, the emails don’t even exist, but I have a rule that any email that doesn’t exist will be forwarded to my actual account. So the made up email I used for LinkedIn was unique and had only ever been typed into the LinkedIn service.
I’ve been doing this for a while, and generally most things don’t seem to lose your email. There have been a few that were probably compromised, they were safe for a while then one day they were lost - this is more likely a malicious actor accessing the website’s database. However LinkedIn is one of only 2 websites I’ve signed up for that have instantly resulted in spam - the other was a porn website.
LinkedIn have always been shady as fuck. When they first started out, they convinced everyone to input their email login details. LinkedIn would then access your email account and send emails to all your contacts asking them to join - all coming directly from your email address, not theirs. That was how LinkedIn built its market share. Back in the MSN Messenger days, LinkedIn emails were pretty notorious, but also everyone was pretty carefree online. They were perhaps one of the first services to demonstrate that you really should be careful what you share online, even if it is a “legitimate” service. Not everyone learned that lesson.
The compromised email thing happend some time after the MSN Messenger days, and I admit that I was one of those gullible baffoons who fell for the login thing initially (I’ve had 3 LinkedIn accounts, my first, then the second which was unique but instantly spammed, then my current). I think the porn website was more or less around the same time as well, so it is possible that LinkedIn was compromised as well as the porn site, such that anyone who signed up for either service (and maybe some others) would instantly get added to a spam list - not by the service but by the malicious infection. However, it certainly would fit their MO for LinkedIn to just sell email addresses directly.
Nowadays, I do get emails to my current LinkedIn account email that clearly should not have been shared. These tend to be more focused on the industry I work in, instead of generic spam. Recruiters almost always contact me via messages.
Don’t give LinkedIn any more information than you have to. In particular, I would encourage users to share their CV’s off platform.
Thanks, it’s rare to find a well thought out answer in here like yours.
I agree that LinkedIn always did shady things to increase their user base. They used dark patterns to get access to your address book even as they got constant criticism for that, both externally and internally. One of their top product managers was actually proud of that, and said that they would have done more if possible.
But I very much doubt they actually sold their customer’s emails at any point. They have always been very protective of their customer’s data, fighting scrapers and limiting APIs. There’s no upside to selling your customers info. You’re undermining your own business by doing so.
and said that they would have done more if possible.
This there is the MO I was talking about.
I can’t conclusively say whether or not LinkedIn intentionally sold my email, or whether they were just infected at the time. However, I feel like the former is at least as feasible, and even if it was the latter it’s still reprehensible of them to be so lax in their security. Like I say, I’ve only experienced 2 websites that did that, and I’ve made up countless emails going on for years before then.
They don’t have lax security. They use industry standard measures, including encryption in transit and at rest, salted passwords (they were caught without salt over a decade ago and fixed it), internal training on security, phishing simulations, the works. Your data is their business, they don’t want to lose it.
Again and again and again and again. I get more spam on my linkedin email address than I do on any other.
I have a set it up so that any email sent to unknown users on my domain gets redirected to email. If you send an email to
bad_address@example.comand my real email isuranibaba@example.com, I will still receive the email.Now this is great because I will just use
name_of_service@example.comand still get the email. If the email is leaked, I will know where it came from.Owning your own domain is great that way. Even makes the little bit I pay to ProtonMail well worth it. There are a few addresses I have dedicated, like my aws@example.com, me@, and my-name@, but the rest just go to a catch all. It’s fantastic.
My mail is hosted by my domain host but I am considering switching to Proton. Have you done such a move?
I made that move and had no issues. You can copy/paste your way through DNS setup and the rest is just configuring your proton account how you want.
You’ll want to be familiar with proton and some of the tradeoffs in its privacy model, but it’s most likely more feature-full than a hosting provider. Dreamhost, for one, is quite basic.
Yeah the setup is pretty trivial and it works great.
Be careful, my domain got on a whole bunch of ISP’s spam lists because I had done the same thing.
They really don’t like open domain email working.
That’s annoying! It’s not been my experience, out of curiosity do you have any theories why your domain/aliases got blocked?
out of curiosity do you have any theories why your domain/aliases got blocked?
For my domain it was put on a spam list that various ISPs use.
When I spoke with one ISP they said it’s because I had an open email address situation going, where a spammer can send a spam email out to a third party and on the reply address to they can make up anything as an email address for my domain name and it would be ‘valid’ because my domain email server was set up to receive all emails that you described.
And because of that I got put on a global spam list which many ISPs use. At the time I didn’t even know about my domain being on the list, I just noticed a big drop in emails I was receiving.
FYI this happened over a decade ago, so I do not know if that is the current practice today. But better to make sure any email addresses to your domain that is not valid does not go through. No “catch all” bucket situation.
That’s not because you have a wildcard. That’s because you need to implement DKIM, DMARC, and SPF records to prevent others from using your domain name to send mail.
MTAs use those standards to verify if somebody is permitted to send email for your domain. If you don’t have those set then you can get what that ISP described.
That’s because you need to implement DKIM, DMARC, and SPF records to prevent others from using your domain name to send mail.
Well I used a third party service to host my domain, and as far as I can remember (like I said this was over a decade ago, maybe almost two decades), everything was set up correctly at that time.
Not trying to dispute what you said, but I can at least speak towards that as far as we knew at the time we had the domain set up correctly on our end, the stuff we could control.
The only thing is we had a catch-all bucket setting turned on for emails to be forwarded to an internal email address of our domain.
There has never been a correct way to deploy these services, just increasingly complex, featurefull, and or secure ways to do it
I ended up just disabling the alias I use to receive emails from LinkedIn. Since I noticed I just kept deleting those emails without ever reading them, I figured I’d just opt to not receive any emails. :D
According to Troy Hunt this alleged leak is mostly from older leaks and fake data:
“this data is a combination of information sourced from public LinkedIn profiles, fabricated emails address and in part (anecdotally based on simply eyeballing the data this is a small part), the other sources in the column headings above. But the people are real, the companies are real, the domains are real and in many cases, the email addresses themselves are real”
Source: https://www.troyhunt.com/hackers-scrapers-fakers-whats-really-inside-the-latest-linkedin-dataset/
That would explain the targeted scams I’ve been subjected to which seem to have been coming from old colleagues
Now I know why I’m getting scam mails on the email address that I never use online and scam phonecalls on the phone number I never use online, except for LinkedIn.
Gadammit, my linkedin uses my clean email account. Linkedin security, do better!
So glad that I did NOT simply close my account there, but instead I changed every single piece of personal data to some meaningless xyz123 before I finally closed it.
Your old info is still backed up there
Yes, but it was a while ago, and the backup gets older every day.
Was surprised at first, then I went to go log in to change my password.
And then it said I was emailed a 2FA code… the code was part of the email header.
Now I’m completely unsurprised this happened.
I’m not sure what you’re implying here regarding headers? Email is insecure regardless; even when using SMTP with TLS, it’s not like the headers are exposed whereas the body would be encrypted or something.
well with PGP, the header is unencrypted. But even with just smtp, the issue is simpler.
Putting it in the header makes it more accessible.
various emails could have the header “Is this you?”, and not all of them will hold a 2fa code, and even if they do, they may time out before you can find it and use it.
But if the email has the header: “Your secure 2fa code is 123456” from “noreply@example.com”
then unsurprisingly, logging into example.com with the user’s email and that 2fa code is going to be a breeze.
well with PGP, the header is unencrypted
Is there a single large company that even sends PGP email?
logging into example.com with the user’s email and that 2fa code is going to be a breeze
Sure, IF 1. you already have the user’s password, and 2. a new code wouldn’t be required/the previous code invalidated when initiating a new login session?
Like, I’m not saying that 2FA codes via email is secure, but you’re implying that they are making a security hole via this - which I don’t see.
Pgp, the greatest program never used by anyone
I used it. For about 10 minutes. Then I read the help files. Then I searched. Then I used it some more. Then I uninstalled it.
Unless you followed by installing gpg… then you failed. There are tons of uses for it, not necessarily encrypting emails (or more precisely, it kind of sucks at encrypting emails).
Yeah not following the logic. 2FA via email is insecure. Doesn’t matter where in the email. That person is confused about something.
the code was part of the
… part of the Subject header in the encrypted body of the message, you mean? What a nothing-burger.
encrypted body of the message
Encrypted what? LinkedIn lets you add a key/cert to send you encrypted emails?